https://www.perrini.ch/wp-content/uploads/2017/01/gimx_armbian.zip
thiago.perrini
1. Copy the new IOS-Image in the flash memory...
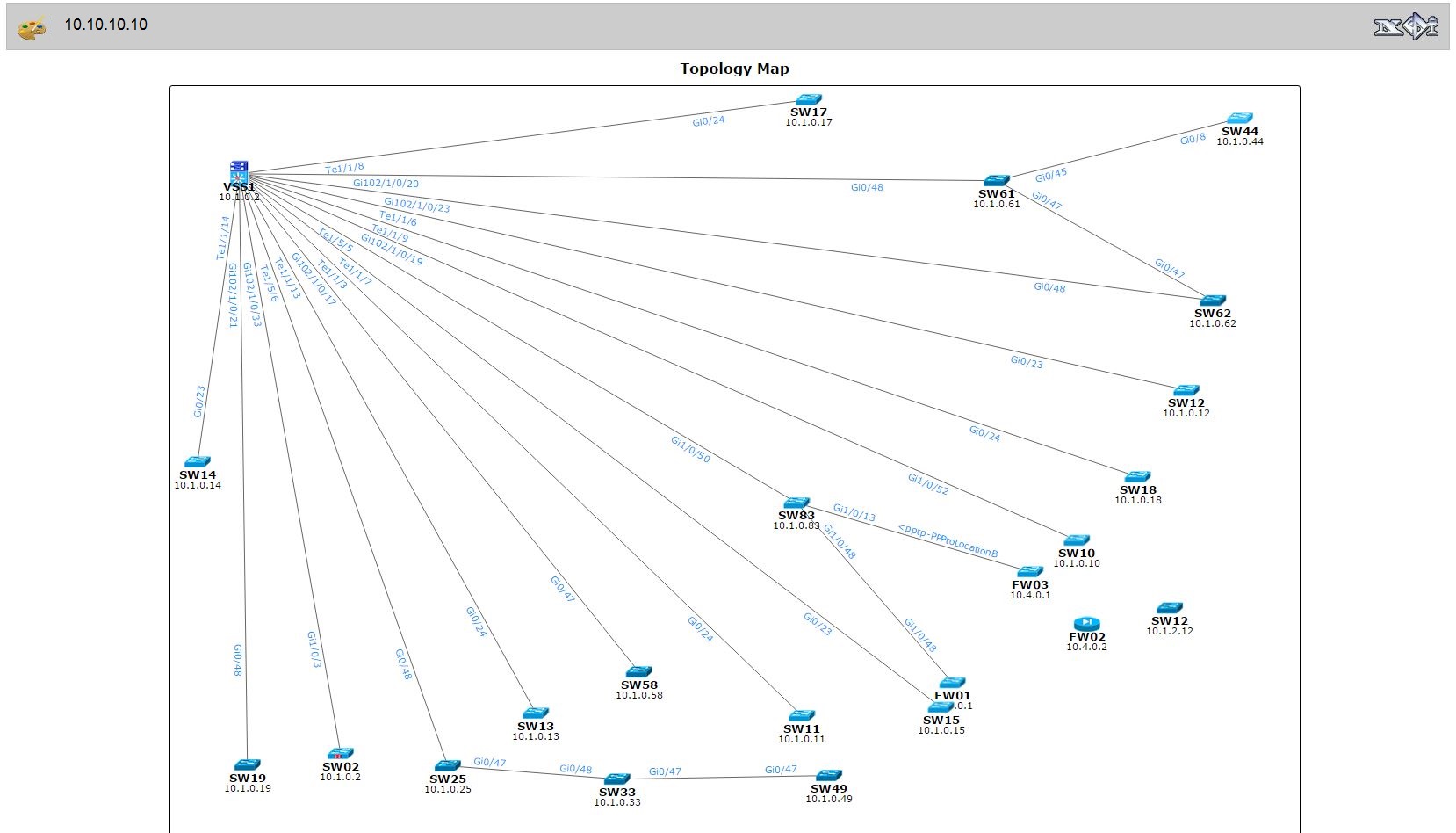
Because of our requirements I have changed the Topology-Map,...
With the Slogan >>Connect the Unconnected<< begins Cisco to...
Today I had some issues on my Laptop with...
To create an image file on Linux we have...
Yeah finaly the cisco NM-8A/S modules where I bought on...
The Shellshock bash bug is a critical security hole...
How to upgrade Cisco IOS-Image over USBflash with a...
Today is the last day to take the legendary...